
One Identity Solutions for Identity and Access Management
One Identity solutions eliminate the complexities and time-consuming processes often required to govern identities, manage privileged accounts and control access.
Purpose and Values
At One Identity, a Quest Software business, we solve complex problems with simple solutions. We deliver technology that eliminates the need to choose between efficiency and effectiveness. We’re committed to helping you get more done in your workday, so you save time and your business saves money.
Our unwavering commitment to you is to:
- Deliver great products
- Provide great service
- Be simple to do business with
In this video, Chairman and CEO Jeff Hawn discusses how our purpose, vision and values guide the way we interact with each other, our customers and partners.
Identity Manager

Take the risk out of enterprise identity and access management
Mitigate risk, secure data, meet uptime requirements and satisfy compliance by giving users access to data and applications they need. Identity and access management (IAM) can be driven by business needs, not IT capabilities. With Identity Manager you can unify security policies and satisfy governance needs— today and into the future.
Features
Risk reducer
Make better security decisions by combining security information and policies from multiple sources to reduce exposure and eliminate information silos
Starling Connect
Extend identity governance capabilities to the cloud and reduce time to onboard new cloud applications.
Governance 360
Provide auditors with detailed, real-time governance reports that includes information about what resources are in your environment, who has access to them, when, and why that access was granted and terminated.
Provisioning done right
Eliminate manual mistakes by automating provisioning to any system, platform or application on premises or in the cloud. Extend provisioning to enterprise applications such as Exchange Online, SharePoint and Oracle E-Business Suite.
Privileged governance
Achieve a unified governance approach for all employees, regardless of their role and level of access. Users can request, provision and attest to privileged and general user access.
Data governance
Get control and visibility of your data
Attestation dashboard
Schedule on-demand or routine attestation and display the status of group or distribution list in a clear, concise dashboard view; and produce detailed reports for discovery, as well as to support compliance.
Password reset
Reset user account passwords and set user-policy preferences that mirror organization’s password rules and requirements. Enables multiple password policies depending user roles.
Multi-factor now
Enable two-factor authentication through Identity Manager with integrated deployment across enterprise applications and integrated with One Identity Starling Two-Factor Authentication (2FA).
Access done right
Enhance security by providing employees, contractors, partners, customers, students, alumni, constituents and patients with only the access they absolutely need – nothing more and nothing less.
Self-service access portal
Save time and reduce IT effort via a customizable online ‘shopping cart’ portal. Enable users to requests access to network resources, physical assets, groups and distribution lists and control access rights and permissions for their entire identity lifecycle while using predefined approval processes and workflows.
One Identity Safeguard
Securely store, manage, record and analyze privileged access
The methods that hackers use to gain access to your systems and data are constantly evolving. Ultimately, hackers want access to your privileged accounts as they provide unlimited access to systems and data. In nearly every recent high-profile breach, lapses in privileged account management have been exploited. To limit the damage when a breach occurs, you need a secure, efficient and compliant way to provide access to privileged accounts.
Take the stress out of protecting your privileged accounts by securely storing, managing, recording and analyzing privileged access with One Identity Safeguard. Available as a hardened appliance with an intuitive interface, Safeguard can detect and halt unknown threats while satisfying your auditors and admin. It is an integrated solution that combines a secure hardened password safe and a session management and monitoring solution with threat detection and analytics.
Features
Policy-based release control
Using a secure web browser with support for mobile devices, you can request access and provide approval for privileged passwords and sessions. Requests can be approved automatically or require dual/multiple approvals based on your organization’s policy. So whether your policies consider the requestor’s identity and level of access, the time and day of the request attempt, and the specific resource requested – or all of these — you can configure One Identity Safeguard to meet your customized needs. Plus, you can input reason codes and/or integrate with ticketing systems.
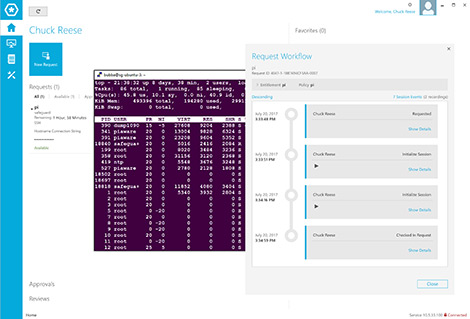
Full-session audit, recording and replay
All session activity – down to the keystroke, mouse movement, and windows viewed – is captured, indexed, and stored in tamper-proof audit trails that can be viewed like a video and searched like a database. Security teams can search for specific events across sessions and play the recording starting from the exact location the search criteria occurred. Audit trails are encrypted, time-stamped and cryptographically signed for forensics and compliance purposes.
Change control
Supports configurable, granular change control of shared credentials, including time-and last-use-based, and manual or forced change.
User behavioral biometrics
Each user has its own idiosyncratic pattern of behavior, even when performing identical actions, such as typing or moving a mouse. The algorithms built into Safeguard for Privileged Analytics inspect these behavioral characteristics captured by Safeguard for Privileged Sessions. Keystroke dynamics and mouse movement analysis not only help you identify breaches, but also serve as a continuous, biometric authentication.
Discovery
Quickly discover privileged accounts or systems on your network with host-, directory- and network-discovery options.
Approval anywhere
Leveraging One Identity Starling Two-Factor Authentication, you can approve or deny requests from anywhere – and with nearly any device — without being on the VPN.
Command and application control
Safeguard for Privileged Sessions supports both black listing and white listing of commands and windows titles.
Instant on
Safeguard for Privileged Sessions can be deployed in transparent mode requiring no changes to user workflows. Acting as a proxy gateway, Safeguard can operate like a router in the network – invisible to the user and to the server. Admins can keep using the client applications they are familiar with, and can access target servers and systems without any disruption to their daily routine.
RESTful API
Safeguard uses a modernized API based on REST to connect with other applications and systems. Every function is exposed through the API to enable quick and easy integration regardless of what want to do or which language your applications are written.
One Identity Hybrid Subscription
Expand the capabilities of Safeguard with the One Identity Hybrid Subscription, which offers immediate access to cloud-delivered features and services. These include all-you-can-eat Starling Two-Factor Authentication to protect Safeguard access and Starling Identity Analytics & Risk Intelligence for Safeguard to pre-emptively detect risky users and entitlements. A single subscription enables all One Identity solution deployments.
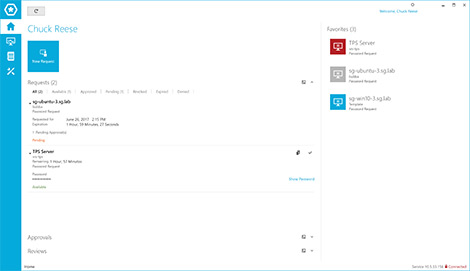
One Identity Safeguard for Privileged Passwords
One Identity Safeguard for Privileged Passwords automates, controls and secures the process of granting privileged credentials with role-based access management and automated workflows. The user-centered design of Safeguard for Privileged Passwords means a reduced learning curve. Plus, the solution enables you to manage passwords from anywhere and using nearly any device. The result is a solution that secures your enterprise and gives your privileged users a new level of freedom and functionality.
One Identity Safeguard for Privileged Sessions
With One Identity Safeguard for Privileged Sessions, you can control, monitor and record privileged sessions of administrators, remote vendors and other high-risk users. Content of the recorded sessions is indexed to make searching for events and automatic reporting simple so you can easily meet your auditing and compliance requirements. In addition, Safeguard for Privileged Sessions serves as a proxy, and inspects the protocol traffic on the application level and can reject any traffic that violates the protocol – thus it is an effective shield against attacks.
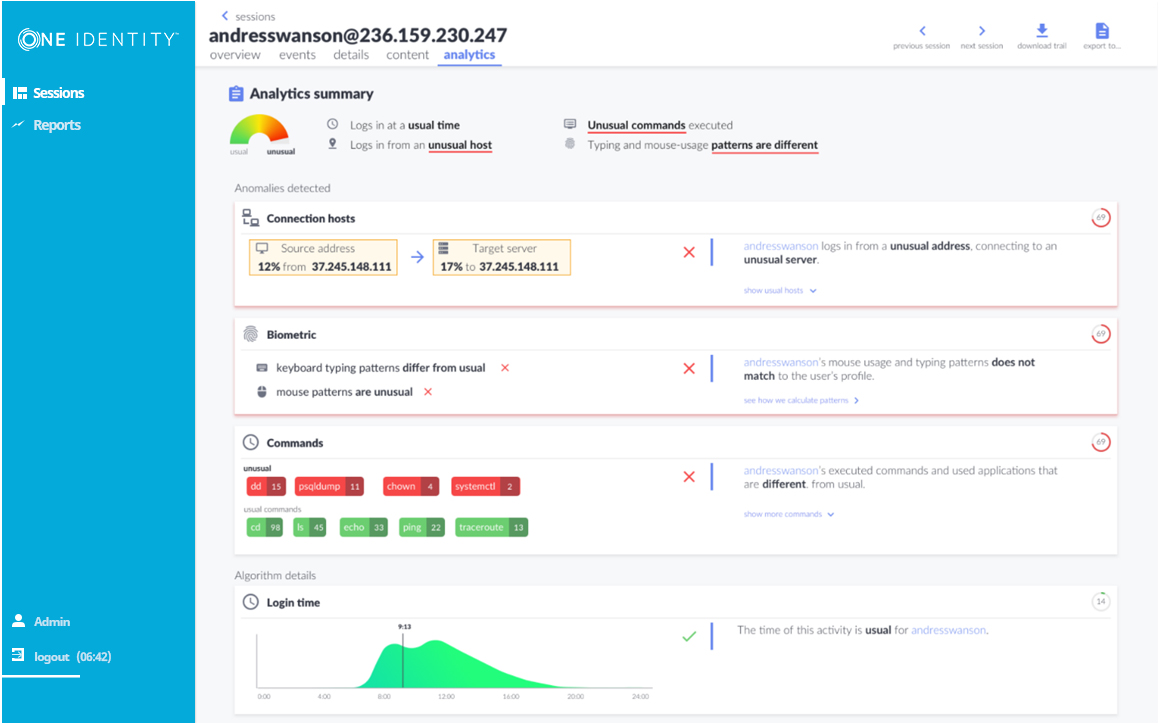
One Identity Safeguard for Privileged Analytics
With One Identity Safeguard for Privileged Analytics, you can know who your high-risk privileged users are, monitor questionable behaviors and uncover previously unknown threats from inside and outside of your organization. By using user behavior analytics technology, Safeguard for Privileged Analytics detects anomalies and ranks them based on risk so you can prioritize and take appropriate action — and ultimately prevent data breaches.
Starling Identity Analytics & Risk Intelligence
On the Board – Identity Analytics | Get Smarter About Risk
Actionable Insights – Get smarter about risk
Support your organization’s digital transformation with a solution that enables you to detect threats and efficiently inspect anomalies so that you can make decisions, prioritize actions and remediate risk.
With Starling Identity Analytics & Risk Intelligence (IARI), you can reduce risk, and thus your attack surface, before bad behavior impacts the business. Accomplish this by eliminating unnecessary or dormant entitlement grants before someone can abuse or exploit them. Starling IARI exposes risk and access behavior enabling faster and improved security decision-making.
Features
Data Source Modules and Collector
Automates the gathering, processing and transmission of entitlement data; enhances security; and enables rapid addition of data sources.
Risk Classification Rules (RCRs)
Collects and processes entitlement grants into groupings and classifications which provides a baseline that can be used to identify high-risk areas. RCRs can be customized to organization-specific settings.
User Risk Profile
Evaluates entitlement grants against the risk classification rules to identify high risk accounts. Changes to an accounts risk profile triggers an alert and can be further validated with a business verification.
Alerting
Proactive notifications when changes to entitlement grants move a user’s profile into a high-risk status (either default or customized).
Business Verification
Provides administrative visibility on entitlements when a change to a user’s risk profile occurs. Enables profile owner to analyze and evaluate role certifications for security threats to the organization.
Access Comparison and Peer Group Analysis
Compares users and peer groups within — and across — organizations to identify the most common collection of users and entitlements, and to highlight differences. Accelerates entitlement remediation by guiding security and risk professionals to where they should focus their efforts.
Entitlement Usage Analysis
Identifies dormant access to reduce risk surface and by initiating governance and/or remediation activities to determine if any action is needed.
Analytical Dashboards and Reports
View compliance and operational dashboards and reports based on user-identity, access and audit data for increased awareness of potential risk factors.
One Identity Starling (SaaS) Platform
Built on an enterprise-grade secure data center and network architecture compliant with International SOC mandates.
Starling Connect
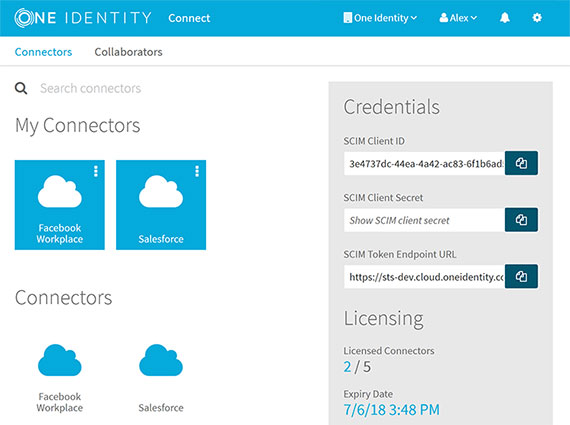
Connect the Cloud
A cloud based, SaaS offering, One Identity Starling Connect extends your current investment in the identity governance capabilities to the cloud and reduces time to onboard new cloud applications. One Identity Starling Connect builds on One Identity Manager or other IAM systems to unify governance, extend access controls, ensure compliance and reduce the time it takes to provision/de-provision users.
Starling Connect:
- Unifies governance for on-premise, hybrid and cloud deployments
- Simplifies compliance for access activities and policies
- Accelerate deployment of new applications – and the provisioning and de-provisioning of users
Features
Unify All
Unify security policy information from multiple sources to mitigate security risks. Operate in a hybrid model to extend provisioning and synchronize cloud applications‘ users, groups (including group memberships) and containers based on a standardized SCIM v.2.0 schema.
Connect All
Reduce the time it takes to onboard cloud target applications seamlessly into your IAM lifecycle and governance processes And eeliminate the hassle of custom coding.
Govern All
Provide real-time governance reports that detail which resources are in your environment (on-premises, hybrid and cloud), who has access to them, and when and why that access was granted or terminated.