
The world’s best visibility, protection,
and response.
See it. Stop it. Secure it.

Expose Hidden Risks
Superior visibility into risky activity, suspicious traffic, and advanced threats helps you regain control of your network.

Stop Unknown Threats
Powerful next-gen protection technologies like deep learning and intrusion prevention keep your organization secure.

Isolate Infected Systemss
Automatic threat response instantly identifies and isolates compromised systems on your network and stops threats from spreading.


See Hidden Risks and Threats
Like you’ve never seen before
Sophos XG Firewall provides unprecedented visibility into your network, users, and applications directly from the control center. You also get rich on-box reporting and the option to add Sophos iView for centralized reporting across multiple firewalls.
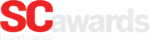
- See endpoint health status and systems at risk
- See all unidentified applications on your network
- See the results of suspicious payloads being sandboxed
- See the presence of any advanced threats on your network
- See your top risk users based on their recent activity
- Drill down to see details on the source of the threat or risk
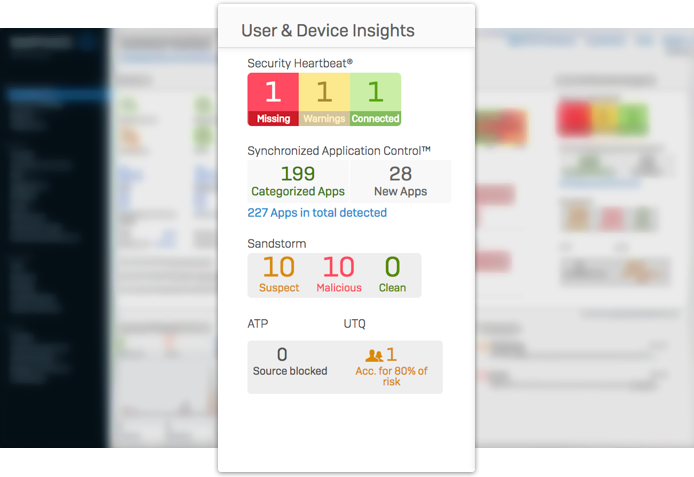
- See cloud services and applications
- Quickly identify unsanctioned Shadow IT
- See recent web and application usage
- Drill down to see detailed reports
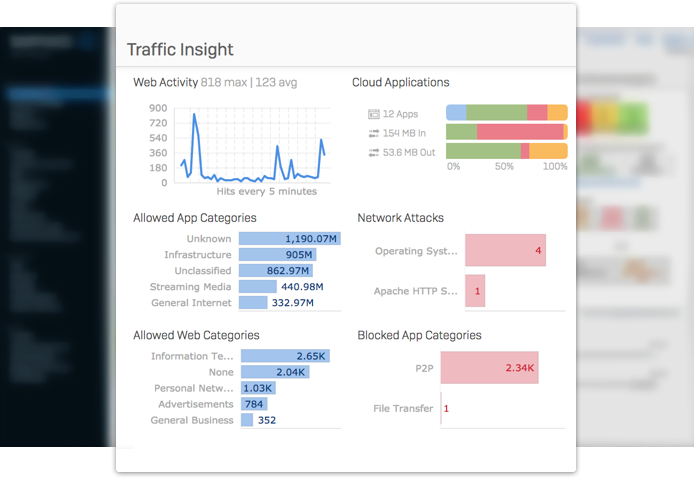
- See a real-time view of system status
- See indicators for performance, services, interfaces, & VPN connections
- See active RED devices, wireless access points, & connected users
- Drill-down to see details and troubleshooting tools
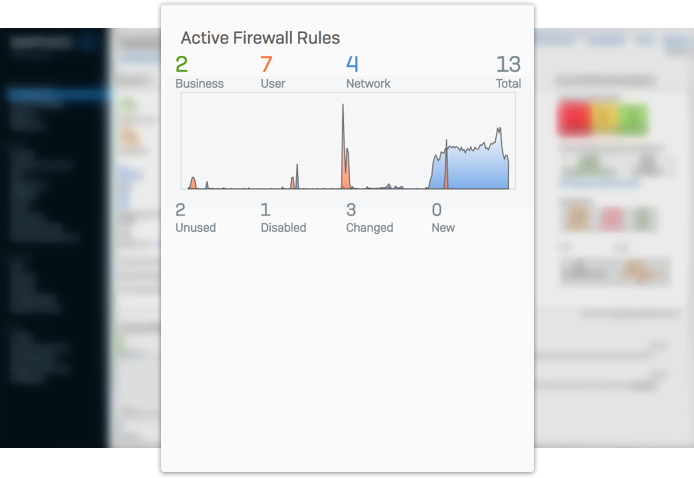
- See how many rules you have by type and status
- See a visual representation of traffic flows by traffic type
- Drill down to see your firewall rules and security policies
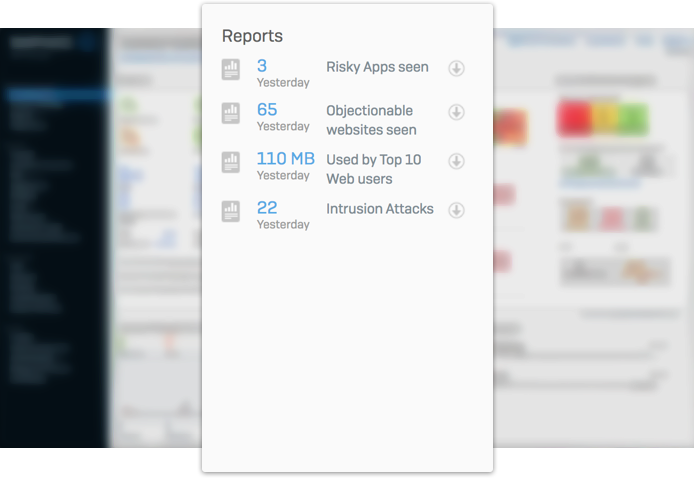
- See the top five risk related reports and their key metrics
- See applications, objectionable websites, top users, and intrusion attacks
- Drill down to see the full report
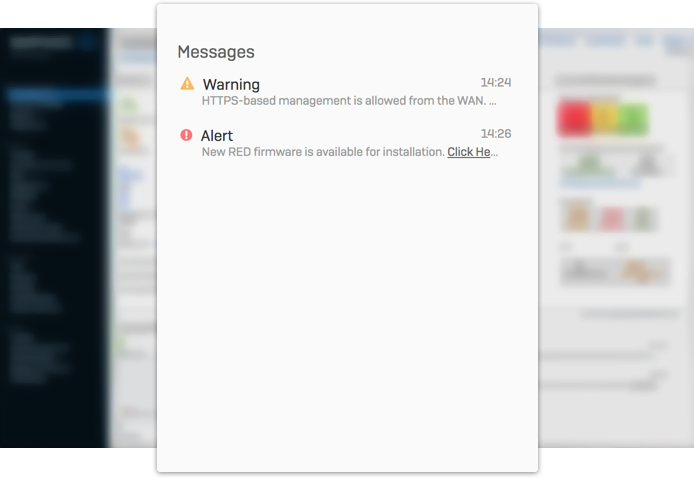
- See important messages and system notices
- See messages about device access, registration, licensing, & firmware updates.
- Drill down to see the full details and take action
Take it for a test drive.
Demo all XG Firewall’s features – no install, no commitment.

Stop unknown threats. Dead.
XG Firewall offers the best protection against the latest advanced threats like ransomware, cryptomining, bots, worms, hacks, breaches and APTs.
- Powerful Sandstorm sandboxing
- Deep learning with artificial intelligence
- Top performing IPS
- Advanced threat and botnet protection
- Web protection with dual AV, JavaScript emulation and SSL inspection
Powered by Deep Learning
An industry first, XG Firewall integrates Deep Learning technology into our Sophos Sandstorm sandboxing. It’s been developed by data scientists at SophosLabs to deliver the industry’s best detection rates without using signatures. It catches previously unseen malware lurking in suspicious payloads quickly and effectively. It’s just one of the ways that XG Firewall stops unknown threats dead in their tracks.

Intercepting Exploits
XG Firewall integrates some of the best technology from our leading Intercept X next-gen endpoint protection like exploit prevention and CryptoGuard Protection to identify malware exploits and ransomware before it gets on your network. Combined with our top performing Intrusion Prevention System (IPS) it doesn’t matter whether a hacker is trying to exploit a network vulnerability or an endpoint vulnerability, XG Firewall will stop it cold.
Keep Your Network Under Control
A breakthrough in application visibility and control.

Synchronized App Control
Automatically identifies hundreds of unknown, evasive, and custom Windows and Mac applications to easily prioritize the apps you want, and block the ones you don’t

CASB and Cloud App Visibility
Cloud Application Visibility identifies all browser applications and cloud services to identify Shadow IT and data at risk to get it under control quickly and easily
Isolate Infected Systems
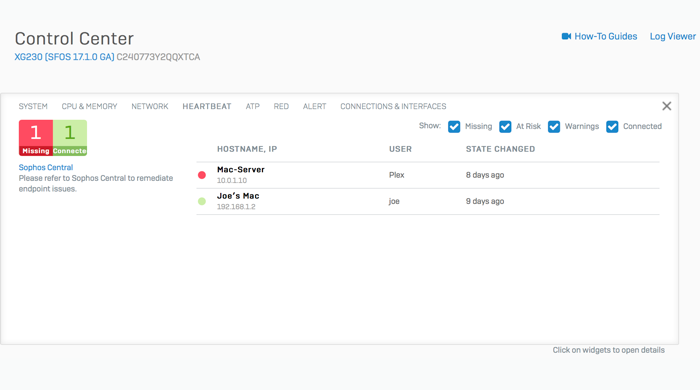
Sophos XG Firewall is the only network security solution that is able to fully identify the source of an infection on your network and automatically limit access to other network resources in response. This is made possible with our unique Sophos Security Heartbeat™ that shares telemetry and health status between Sophos endpoints and your firewall.

Monitor Network Health
XG Firewall not only monitors host network activity, but also receives health status directly from your endpoints so you have constant visibility into the health of your entire network.

Identify Infected Systems
XG Firewall instantly alerts you to compromised systems on your network with full details including the IP address, the user, and the process, so you’re not left digging for information.

Automatically Isolate Infections
XG Firewall uniquely integrates the health of connected hosts into your firewall rules, enabling you to automatically limit access to sensitive network resources from any compromised system until it’s cleaned up
A Firewall That Thinks Like You
So you don’t need to think like a firewall.
We’ve rethought the way firewall rules and security policies are managed. Sophos XG implements an all-new powerful and flexible unified security and control model that enables you to see and manage all your user, application and network policies in a single place on a firewall rule basis.
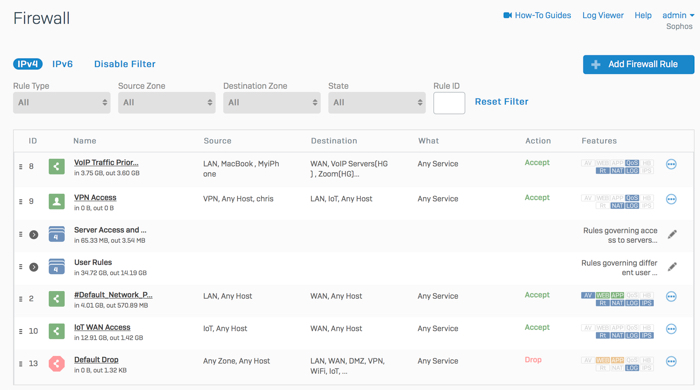
Most firewall products will have you setting up and managing security across multiple modules or screens. Not Sophos. We provide a powerful unified security model that allows you to easily establish and manage your security posture in one place.
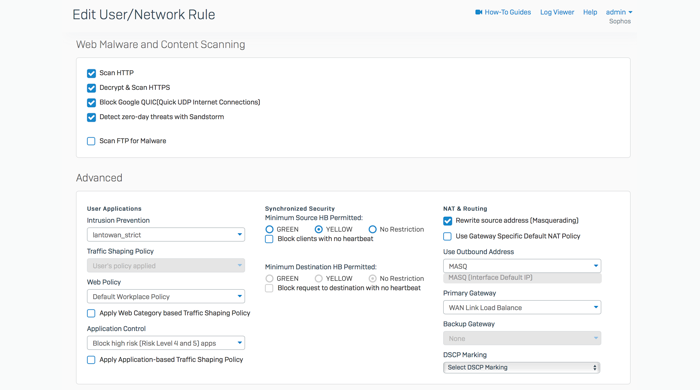
XG Firewall offers industry leading authentication options and enables user-level enforcement for threat protection, sandboxing, application control, traffic shaping, web filtering policy, IPS protection, Security HeartbeatTM and routing – all on a single screen to make management simpler and easier.
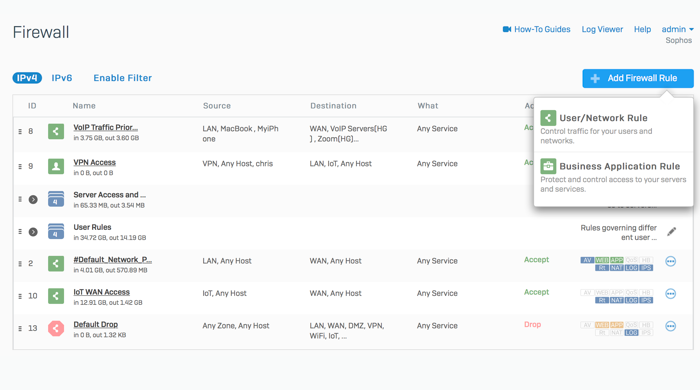
XG Firewall makes it easy to manage all your network security in one place including your network and user-based firewall rules alongside all your web application firewall protection for business applications and servers, as well as your NAT rules.
An industry first, Sophos Security Heartbeat links your endpoints and your firewall to combine their intelligence to immediately identify systems compromised by advanced threats, enabling you to establish policies that automatically isolate or limit infected systems until they can be cleaned up.

If you’re like most network admins, you’ve probably wondered whether you have too many firewall rules, and which ones are really necessary and which ones are not actually being used. With Sophos XG Firewall, you don’t need to wonder anymore
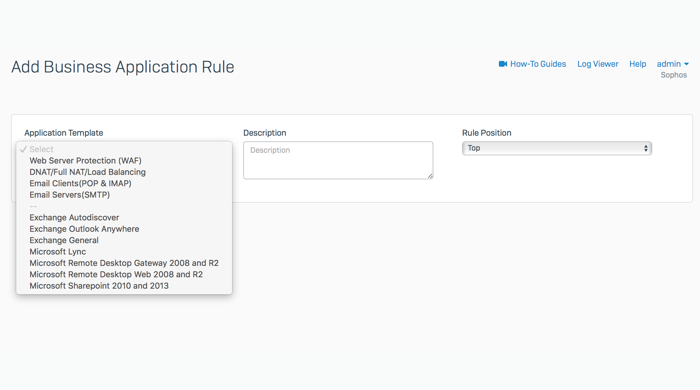
Pre-defined policy templates let you protect common applications like Microsoft Exchange or Sharepoint fast. Simply select them from a list, provide some basic information and the template takes care of the rest. It sets all the inbound/ outbound firewall rules and security settings for you automatically.
Complete Next-Gen Protection
All the advanced networking, protection, user, and app controls you need to stay secure and compliant.
Management
Status and Alerts
The all-new, carefully crafted control center analyzes extensive back-end data sources to surface just the information you need to respond quickly to changes in your network.
- Instant insights at a glance for all your important system, security and network status indicators from the all-new control center
- Automated report analysis highlights reports in the control center featuring data of interest or that may need attention, with one-click access to the full report.
- Quick drill-down interaction with any control center widget to get more detailed information, access relevant tools, or quickly take action.
- Email notifications are automatically sent for important system status events.
- SNMP with a custom MIB and support for IPSec VPN tunnels to manage remote office firewall devices.
Reporting and Logging
Take advantage of the XG Firewall’s extensive on-box reporting or utilize Sophos iView for comprehensive, centralized reporting across your all your firewall devices.
- On-box reporting comes standard with every XG Firewall for all your local firewall reporting needs.
- Centralized reporting aggregates log data across all your firewall devices (including XG Firewall, UTM 9, and Cyberoam devices) to provide comprehensive consolidated reporting from a single screen.
- User and app risk analysis reports such as our unique User Threat Quotient or App Risk Score identify top risk users and applications respectively.
- Live log viewer, accessible from any screen, provides a real-time view into activity in your firewall across all areas of the firewall with powerful search and filter options.
- Change control and audit logging are provided to ensure compliance.
- Syslog support enables safe backup, archival, and analysis of system logs.
USER & APP CONTROL
User Identity
User identity-based policies and unique user risk analysis give you the knowledge and power to regain control of your users before they become a serious threat to your network.
- User identity powers all firewall polices and reporting, enabling unprecedented next-gen control over applications, web surfing, bandwidth quotas, and other network resources.
- User Threat Quotient (UTQ) identifies the top risk users on your network based on their recent network behavior.
- Flexible authentication options including directory services (AD, eDirectory, LDAP), NTLM, RADIUS, TACACS+, RSA, client agents, or captive portal.
- Two-factor authentication (2FA) one-time password support for access to key system areas, including IPsec and SSL VPN, the user portal, and the web administration console.
Application Control
Complete application visibility and control over all applications on your network with deep-packet scanning technology and Synchronized App Control that can identify all the applications that are currently going unidentified on your network.
- Visibility and control over thousands of applications via customizable policy templates with granular controls and smart filter lists that enable you to build custom policies based on category, risk, technology, or other characteristics.
- CASB cloud app visibility identifies all browser applications and cloud services to identify Shadow IT and data at risk to get it under control quickly and easily.
- Synchronized App Control provides a breakthrough in network visibility by identifying all the applications that are unknown, unidentified, or generic on your network enabling you to classify and control them. Prioritize the apps you want and block the ones you don’t.
- User-based application policies enables custom-tailored application control to be added to any user, group, or network policy with the option to also apply traffic shaping.
- Traffic shaping (QoS) prioritizes bandwidth allocation to critical applications and limits bandwidth for non-business applications.
Web Control
Full visibility and control over all your web traffic with flexible enforcement tools that work the way you need, with options for user and group enforcement of activity, quotas, schedules, and traffic shaping.
- Enterprise Secure Web Gateway (SWG) policy model with hierarchical inheritance enables sophisticated group and user-based web filtering policies to be defined quickly and easily, dramatically reducing firewall rule count.
- Template-driven activity control with predefined workplace and compliance policies utilize over 90 predefined website categories, covering billions of pages maintained by SophosLabs with the option to import custom URL lists.
- Traffic shaping (QoS) prioritizes bandwidth allocation to critical web applications and limits bandwidth for non-business websites.
- Comprehensive enforcement monitors HTTPS encrypted traffic, blocks anonymizing proxies, and can enforce Google Apps domains and SafeSearch to ensure your policies are always enforced.
- Potentially unwanted app control protects your network from cryptomining and cryptojacking embedded in websites as well as a variety of other unwanted web borne applications
Content Control
Flexible, user-based monitoring and control of keyword content and downloadable content, including files types via FTP, HTTP, or HTTPS.
- Web keyword monitoring can log and dynamically block content matching uploaded keyword libraries regardless of the site category to help identify problematic or risky behavior related to topics like self-harm, radicalization, bullying, and more.
- File download filtering templates let you control hundreds of different files, executables, and dynamic content types simply as part of any user or network web control policy.
- Outbound email DLP that’s policy-based can automatically trigger encryption or block/notify based on the presence of sensitive data in emails leaving the organization.
- Web caching reduces bandwidth consumption by caching supported web content and downloads, including Sophos Endpoint updates.
PROTECTION
Firewall
Stateful and deep-packet inspection for all network traffic with top-performing IPS and dual-engine AV performance and effectiveness.
- Advanced next-gen IPS protection provides the ultimate network exploit prevention, protection and performance. It supports a uniform signature format backed by SophosLabs.
- Dual-engine AV scanning offers the option of scanning traffic with the Sophos engine for excellent performance and protection, or adding a second engine scan for even more protection.
- Perimeter defenses stops attacks on your network, including reconnaissance detection, spoofing, flood protection (DoS, DDoS), and packet-based attacks (ICMP).
- Country-based policy blocks Geo IP ranges for entire countries or regions.
Sophos Sandstorm Cloud Sandbox
Sophos Sandstorm uses next-gen cloud-sandbox technology with the best technology from Intercept X, providing your organization with the best protection against zero-day threats like the latest ransomware and targeted attacks coming in through phishing, spam, or web downloads.
- Cloud delivery means Sandstorm is fully integrated with your XG Firewall and requires no additional hardware.
- Identifies suspicious payloads such as PDFs, Office Docs, and executables entering the network via email or the web and sends those to the cloud sandbox for extensive machine learning based analysis and remote execution to convict zero-day payloads before they enter your network.
- Powered by deep learning and other technology from our leading Intercept X next-gen endpoint product including exploit detection and CryptoGuard protection stops zero-day threats before they get on your network.
- Great value, affording you all the benefits of enterprise-grade protection without the enterprise price tag.
- Detailed threat reports for every incident so you know exactly what’s going on.
Anti-malware
Sophos’ award-winning, high-performance anti-malware engine is backed by SophosLabs and a 30-year history of protecting enterprises from the latest threats.
- Advanced malware protection that goes beyond signature-based detection to include advanced, proprietary techniques like code emulation and behavioral analysis to detect obfuscated or polymorphic threats.
- Live Protection is exclusive to Sophos and closes the gap between regular updates through real-time cloud lookups.
- Dual-engine scanning offers the option of scanning traffic with the Sophos engine for excellent performance and protection, or adding a second engine scan for even more protection.
- SophosLabs 24/7 global threat research operation is one of few in the world with the breadth and depth necessary to stay ahead of the latest threats.
Web Protection
Sophos’ Web Protection engine is backed by SophosLabs and includes innovative technologies required to identify and block the latest web threats.
- Advanced Web Protection combines advanced analysis capabilities such as JavaScript emulation, behavioral analysis, and origin reputation to protect against modern, multi-stage web attacks.
- Pharming protection guards against phishing and pharming attacks by overriding corrupt host file or DNS lookups.
- HTTPS scanning deep scans encrypted traffic for threats and compliance.
- Potentially unwanted app control protects your network from cryptomining and cryptojacking embedded in websites as well as a variety of other unwanted web borne applications.
- SophosLabs, the global, round-the-clock threat research operation, identifies thousands of newly infected websites and instances of web malware, ensuring you have the best malicious site database protecting your network and users.
Advanced Threat Protection
- Security Heartbeat links your endpoints and your firewall, combining their intelligence to identify and isolate systems compromised by advanced and previously unknown threats.
- Multi-layered, call-home protection combines analysis from DNS, IPS, web, and traffic filters to identify and block botnet and command-and-control (C&C) call-home attempts.
- Intelligent firewall policies account for endpoint behavior to automatically isolate or limit access to infected systems that may be compromised by an advanced threat.
- Traffic light style indicators provide immediate identification of systems at risk with deep drill down into the device, user, and process responsible.
Synchronized Security
- Security Heartbeat: XG Firewall monitors the Security Heartbeat status of all your Sophos Endpoints, enabling you to quickly identify compromised systems and automatically limit network access for these systems until they can be cleaned up.
- Destination Heartbeat Protection, controls access to endpoints and servers based on the status of their Heartbeat – further bolstering protection from potentially compromised systems until they are completely safe.
- Synchronized App Control a breakthrough in network visiblity, utilizes the Synchronized Security relationship to automatically identify, classify and control unknown applications on your network.
Business Applications
- Next-generation IPS provides advanced protection from hacks and attacks while maintaining top performance.
- Web Application Firewall integrates seamlessly with your next-gen firewall, combining industrial-strength protection like URL and form hardening with the ease of template-driven policy configuration.
- Granular, user-based protection with a rich set of configuration options and multiple authentication options, ensuring easy access for those you want and powerful protection from those you don’t.
Email and Data
- Full MTA store and forward support enables business continuity, allowing the firewall to store mail when target servers are unavailable.
- Live anti-spam provides protection from the latest spam campaigns, phishing attacks, and malicious attachments.
- SPX encryption is unique to Sophos, making it easy to send encrypted email to anyone, even those without any kind of trust infrastructure.
- DLP that’s policy-based can automatically trigger encryption or block/notify based on the presence of sensitive data in emails leaving the organization.
- Self-serve user portal gives employees direct control over their spam quarantine and block/allow lists, saving you time and effort.
NETWORKING
Routing and Bridging
- Powerful object-based NAT rules enable multiple ports and services to be forwarded in a single rule with a number of pre-defined cloud service host objects making NAT rules easy and intuitive.
- Access control criteria is based on user identity, source and destination zone, MAC or IP address, Service, etc.
- Advanced routing uses Static, OSPF, BGP, and RIP with full 802.1Q VLAN support and multicast with support for per-rule routing and policy-based routes based on source, service, or destination.
- WAN link balancing provides load balancing and high availability with weighting options and fail-over rules.
- Flexible bridging options allow device ports to be bridged to share a common address space, and fail-open bypass ports allow bridged inline deployments with no disruption.
- IPv6 Certified support throughout for interfaces, routing, and tunneling, including 6-in-4, 6-to-4, 4-in-6, IPv6 rapid deployment (6rd), and IPv6 through IPSec tunneling.
Segmentation
- Zones rise above the traditional interface-based configuration model to provide a more intuitive, powerful, and simple way to secure and segment your network and create policy.
- Default zones for LAN, WAN, DMZ, LOCAL, VPN, and Wi-Fi make it easy to get up and running quickly and easily with support for custom zones on the LAN or DMZ.
- Full VLAN support provides powerful segmentation options by trust, traffic type, location, and other criteria across your physical network infrastructure.
- Zone and VLAN isolation ensures zones are isolated until firewall rules are explicitly created to enable secure exchange of application, user, and network traffic to pass between them.
- Zone-based policies enable simple but powerful firewall rules that anyone can immediately interpret and understand.
Traffic Shaping (QoS)
- Network or user-based traffic shaping prioritizes bandwidth allocation to critical applications and limits bandwidth for non-business applications on any network or user-based policy.
- Web category traffic shaping prioritizes bandwidth allocation and/or limits based on website category.
- Network traffic quotas allow unlimited customization for total or individual network traffic quotas.
- Real-time VoIP optimization ensures real-time traffic for Voice over IP and other communications are given prioritization.
Wireless Controller
- Plug-and-play deployment enables quick installation and configuration with just a few clicks since the firewall automatically recognizes the Sophos Wireless Access Point as soon as it’s connected.
- High performance with the latest 802.11ac and powerful radios, offering maximum coverage and throughput.
- Flexible configuration with options for isolation, bridging, zones, hotspots, channel width, and multiple SSIDs per radio.
- Secure encryption with support for all the latest standards including WPA2 personal and enterprise.
Performance
- High performance IPS with among the best security effectiveness.
- High-performance proxy supporting thousands of simultaneous connections enforces web policy with millisecond latency.
- High-speed interfaces and switches come with plenty of GigE ports on every appliance and optional FlexiPort expansion modules for 10GbE copper or fiber connectivity.
- High availability with active-active load balancing or active-passive fail-over and WAN link balancing lets you easily double your performance when you need it.
VPN
Select from a full range of VPN technologies for secure site-to-site and remote access.
- Full standards-based VPN support includes IPSec (with IKEv2 support), SSL, PPTP, L2TP, Cisco VPN (iOS), and OpenVPN (iOS and Android).
- Clientless portal using Sophos’ unique encrypted HTML5 self-service portal provides support for RDP, HTTP, HTTPS, SSH, Telnet, and VNC for quick access to essential business applications.
- RED VPN, a Sophos exclusive, uses an affordable Remote Ethernet Device (RED) at the remote site to easily establish a secure VPN connection.
- Firewall-to-firewall RED tunnels offer a high-performance VPN alternative to connect your firewalls, exclusive to Sophos.
RED VPN
- Plug-and-play VPN. Simply enter the RED ID into your firewall and ship it.
- No technical skills required. As soon as it’s plugged in, the device will automatically establish the VPN connection with the firewall.
- Traffic routing allows you to direct all network traffic from the remote location back to your firewall for complete protection, or to only route inter-office network traffic via RED.
- Secure encryption. All traffic between the RED and your firewall is encrypted to provide a secure private connection
Encrypted Traffic
- SSL decryption securely intercepts and decrypts SSL traffic to allow deep scanning for security, compliance, and policy checks with policy-driven opt-outs, allowing privacy for sensitive traffic.
- SSL inspection ensures enforcement and compliance even without full man-in-the-middle decryption.
- Certificate validation protects your network from malformed or spoofed certificates.
- Protocol enforcement for encrypted traffic connections identifies and blocks unwanted traffic trying to bypass filtering or traffic shaping.
Top Performing Protection
XG Series hardware appliances provide industry leading performance at every price point with the ultimate in flexibility, connectivity and reliability.


Purpose-built to Perform
Built with the latest Intel multi-core technology, generous RAM provisioning and solid-state storage on every model.

Flexible Connectivity to Fit Your Network
We offer a variety of integrated and modular connectivity options to fit every business including WiFi, 3G/4G, DSL, and copper/fiber options up to 40GE.

Business Continuity
High availability deployment options and redundant power supplies and disks to ensure you never miss a bit or a byte.
